Contents
For years, one of the overlooked areas for the Linux desktop was access to “effective” parental controls. Back in 2003, I remember the now defunct Linspire (then known as Lindows) offered a proprietary option called SurfSafe. Surprisingly, at least back then, the product worked very well in providing accurate content filtering capabilities; something that was not,in fact, available and easy-to-use at that time.
Years later, an open-source alternative was released to the greater Linux community known as GNOME Nanny. Fantastic in terms of usage control, its web content web filter was laughably terrible. As expected, crowd-sourcing a filtering list isn’t a great solution. And like SurfSafe, the project is now defunct.
OpenDNS is your friend
Some folks have charged the reason these applications are no longer available simply comes down to the fact that they’re not needed. This is nonsense, as proven by the web content filtering industry for proprietary platforms. People want this functionality, regardless of how you and I may feel about it.
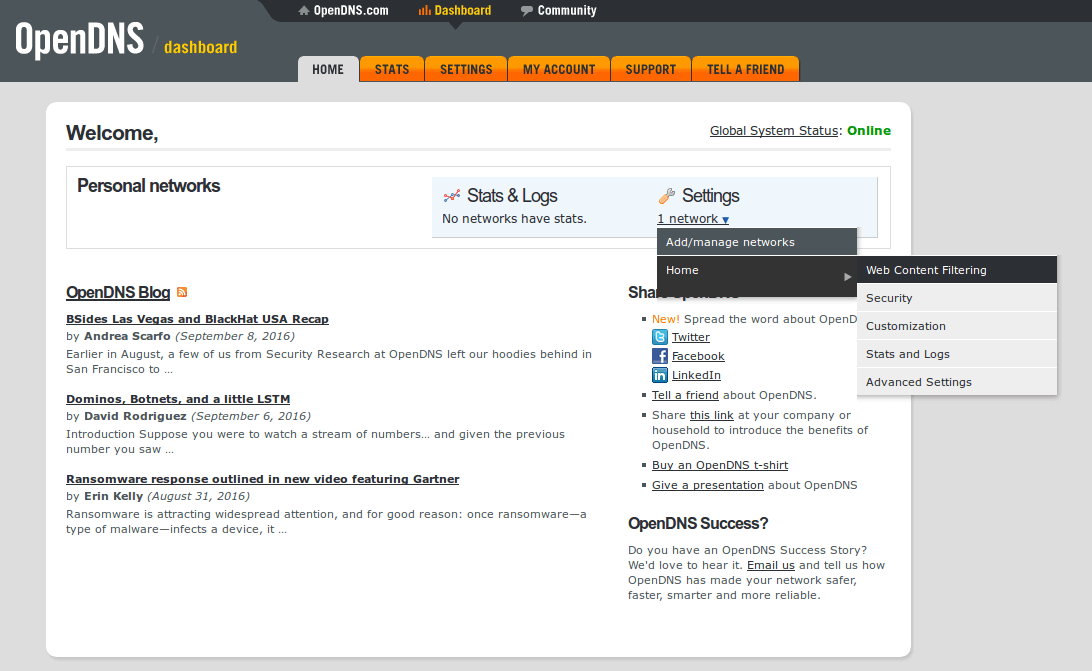
These days, keeping a firm grasp on your home network and PC is as simple as running two simple tools. The first option is provided by OpenDNS. This service not only provides lightning-fast DNS speed for your web browsing, it can also provide excellent content filtering as well.
Not only does OpenDNS provide you with lightning-fast DNS for your Internet surfing needs, it also has the most accurate and advanced content filtering I’ve ever used. Period. While I agree there is value in preventing specific domain access via a hosts file, most people with kids are looking to block content based on the content type, not a domain.
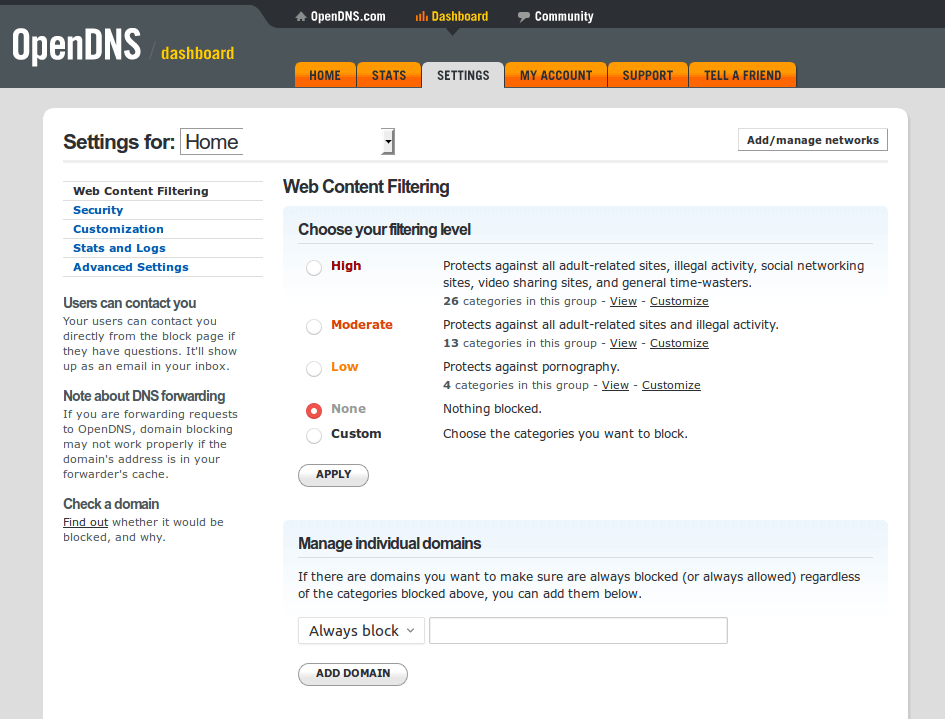
Once you have your content filtering setup the way you want, the next step is to make sure your ISP provided IP address remains correct with OpenDNS. This can be tricky if you’re provided a dynamic IP address. If you don’t know for sure, it’s usually best to ask your ISP.
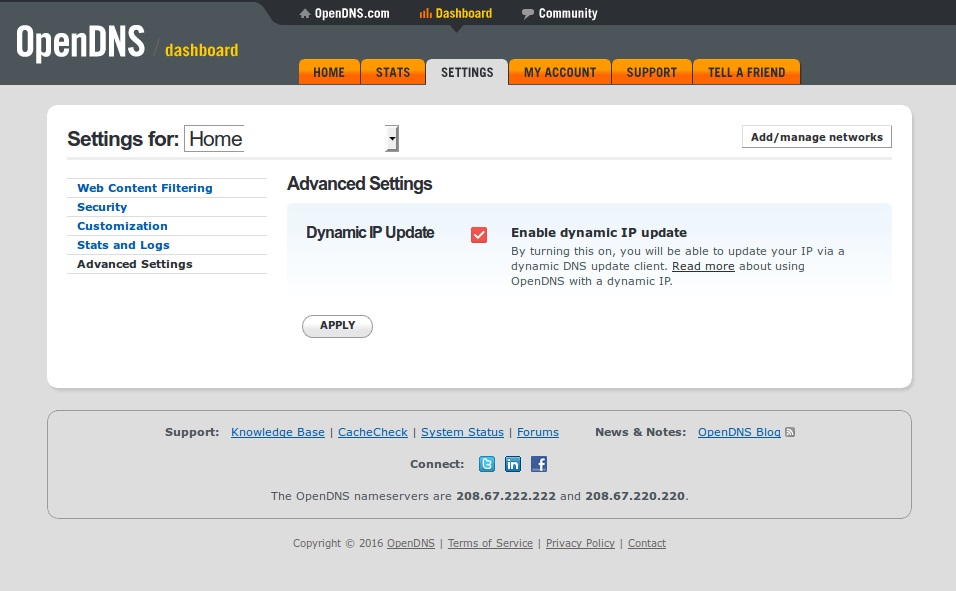
Assuming you have a dynamic IP address, make sure your Advanced Settings for OpenDNS are set up for dynamic IP updates. Next, you need one PC on your network that is turned on most of the time and that can run a small piece of software to ping OpenDNS. This software is called ddclient. You can easily install it from your favorite repo. Before you install it, you’ll also want to make sure you can use SSL with it as well. So do install this first (this assumes you’re using Ubuntu).
sudo apt install ssh libio-socket-ssl-perl
Now you can install ddclient from Synaptic or however else you like.
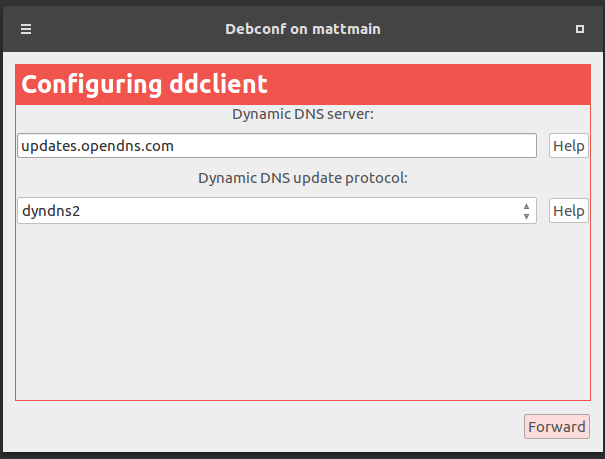
As you install it, you’re going to be presented with the screen below. Using the pull-down menu, select other, then forward.
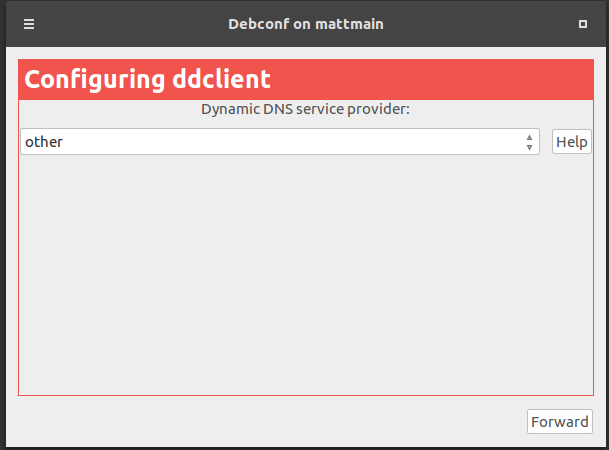
The next screen needs to have updates.opendns.com in the server box and from the pull-down menu, dyndns2 selected. Now click forward like before.
The next part is where you begin entering your username and password for OpenDNS. In my case, my user name is an email address I use just for such login environments.
If you need to change either of these later on, not to worry. On Ubuntu, the config file is available under /etc/ddclient.conf and for other distros, it might be under /etc/ddclient/ddclient.conf – one of these paths will work for you.
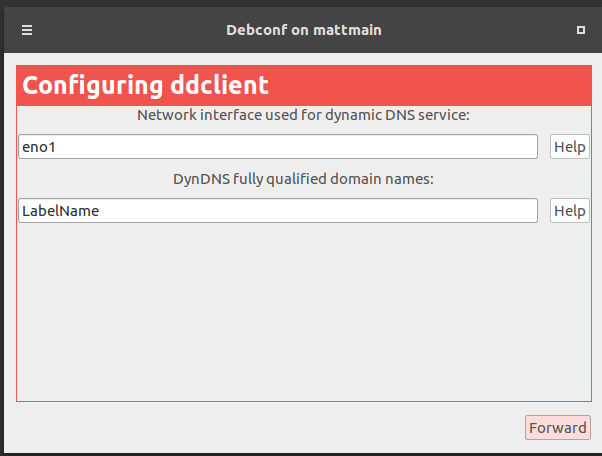
Now this next section can be a little confusing. The network interface device used can be found with:
lshw -C network
or
ip address
Both of these will provide you with something like eth1, eno1 or wlan1 or whatever. With this information, you’ll drop the interface designation into your top box as you see below. The second box isn’t what you might think – it’s actually your OpenDNS label. Back at dashboard.opendns.com/settings/ you’ll notice a Label name for your network. This is what you place into the second box.
Now that everything is done, I recommend using a terminal to double check your work. We’ll use nano for this. Again, this is assuming you’re running Ubuntu.
sudo nano /etc/ddclient.conf
This should look something like:
# Configuration file for ddclient generated by debconf # # /etc/ddclient.conf protocol=dyndns2 use=if, if=eno1 server=updates.opendns.com login=OpenDNS_registered_email password='OpenDNS_password' Label_At_OpenDNS
We’re going to now add the finishing touches to this file by adding this to the very end of it.
daemon=3600 ssl=yes
After typing those two items to the bottom of the file, Ctrl-X to save the file and we’re ready to begin testing this sucker. Use this debugging command, as it will let us know straight away if there are any issues with logging in, etc.
sudo ddclient -daemon=0 -debug -verbose -noquiet
If the results look something like this, ddclient is successfully set up for OpenDNS:
SUCCESS: Home: skipped: IP address was already set to xxx.xxx.x.xx
If instead, you end up with auth errors, remove ssl=yes from the above config and try the debugging command again. If this works, then you need to purge ddclient, then reinstall it again. Now try to reinstall ssh libio-socket-ssl-perl and then reinstall ddclient again. Add ssl=yes to the config and it should work just fine now. Also double check your OpenDNS login and label (from the OpenDNS dashboard).
If the test is successful, the next step (if using Ubuntu or anything with systemd) is to make sure it starts up automatically upon rebooting.
sudo systemctl enable ddclient.service
sudo systemctl start ddclient.service
Then verify everything is running:
sudo systemctl status ddclient.service
Once all of this is done, you will now have ddclient running to ping OpenDNS so it has your most current WAN IP address. With this, OpenDNS can now provide you with whatever content filtering you happen to want to use.
OpenDNS on your router
You could absolutely set things up to where only one PC is using OpenDNS. However, my suggestion is to do it completely or not at all. Remember, blocking one’s PC from content doesn’t block one’s smart phone. If you want to control content filtering across your network, my suggestion is to use your router’s DNS controls and set it to run OpenDNS servers.
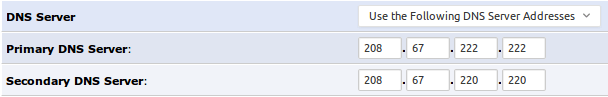
Now each router out there is going to have different settings for this, but all routers have this option buried somewhere. The best bet is to read through your router’s documentation to figure out where this is. I’ve also found rebooting the router and various network devices throughout the house also ensures everything is on the same page with regard to using the correct DNS settings. You would reboot your router after making OpenDNS servers your goto DNS option.
Hosts file blocking
If your need for parental controls isn’t that complex and basically comes down to blocking a couple of websites then you might want to consider utilizing the hosts file on your Linux box. Keep in mind, thiswill only work on the computer on which you set it up. A better network-wide solution that achieves the same result would be to utilize the content restriction capabilities of your home router.
To block websites on a single PC running a Linux distro like Ubuntu, there are few different methods to block domains. The first is to use your hosts file to itemize each domain you wish to block. For example, this would block example.com in your /etc/hosts file.
0.0.0.0 www.example.com 0.0.0.0 example.com ::0 www.example.com ::0 example.com
The above text in your hosts file will completely prevent access to example.com regardess of the browser you use. This is useful for blocking a domain at the PC level, rather than at the network level. Great if you have a kid that needs to be banned from Facebook while still having access to other sites to complete homework.
Network level content filtering
Unless you’re a single computer family, lacking tablets and phones, odds are you might be happier with network content filtering. Even if you’re not trying to filter content from your kids, you can still use this type of content filtering to keep known malicious sites at bay.
The software I like to use for this is called SquidGuard. It’s available both as a standalone application or as a plugin with firewalls like pfSense. Personally, I recommend using SquidGuard through a firewall as you will get more “bang” from the box in question. And yes, you “could” use SquidGuard for a single PC installation, too. Personally, I recommend the firewall/network approach.
Assuming you decided to use pfSense, you simply need to install the SquidGuard plugin and activate it. Simply follow this tutorial to upload a blacklist and complete initial configuration, then you’re all set. So long as you route all of your LAN traffic through the pfSense box, your SquidGuard blacklist will provide you with the content filtering you decide on.
Providing time limits
There are two methods you can utilize to limit when someone has access to a computer using popular Linux distros. The first is to limit Internet access at the router level. How this is done depends heavily on the router itself. Most consumer routers have options for “parental controls” that allow you to put on/off time settings.
Those of you using pfSense can do the same thing by creating a rule set to accomplish the same on/off effect for your network-wide Internet access using Firewall>Schedules to setup the timing you wish to disable Internet.
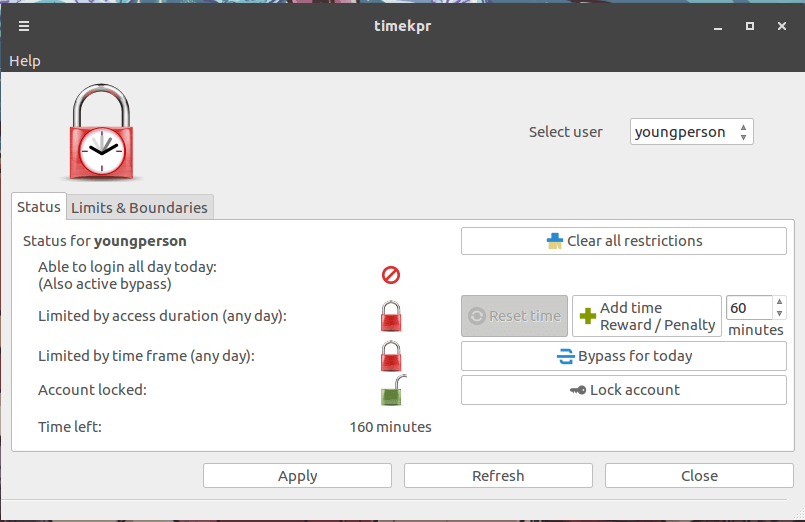
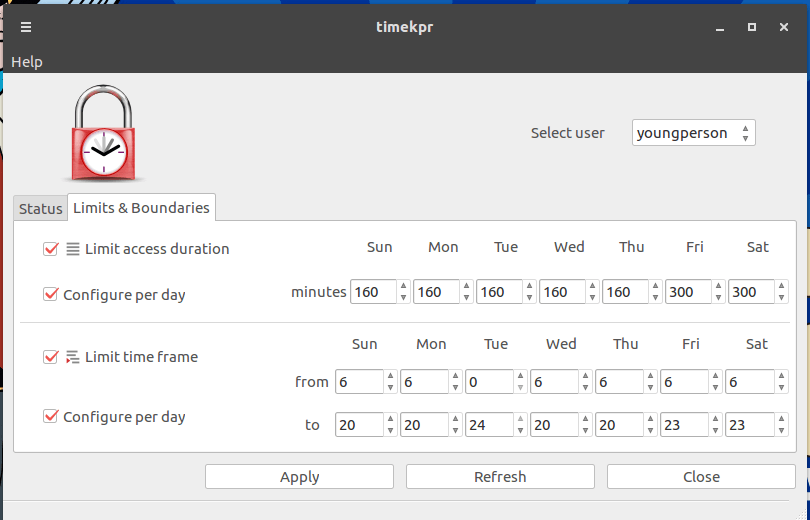
Now if instead you’d like to limit access times to an individual PC, then perhaps using timekpr would be a better option. I’ve found that timekpr is surprisingly robust despite its simple GTK interface. You can use timekpr to limit PC usage based on minutes/hours or from a scheduled time period point of view. Even time based allowances and penalties are possible using timekpr.
What’s the best option?
Since I’m not a parent I can only suggest which tools we have available. However, whether or not to use them is a personal choice that each family needs to figure out for themselves.
That said, I think that’s nice to know that if we need to “put the brakes on” a young person’s PC usage or their surfing habits, the tools are absolutely available for the Linux desktop.



How does this setup interferes with Ubuntu’s own local dns cache service (dnsmasq)?
I’m assuming you mean OpenDNS’s content filtering and local dns cache? Once the local cache is flushed and assuming you’re using OpenDNS with content filtering enabled (on their website), you would then experience blocked content as it’s set up.
I use OpenDNS with pfSense and DNS Forwarder (router level dnsmasq daemon) and have no issues. However, at the local PC level using dnsmasq I have no idea. I’ve never tested dnsmasq with OpenDNS. Some quick research indicates there could be “some” issues with Google queries, however it looks like it’s easily fixed.
https://wiki.archlinux.org/index.php/dnsmasq#Prevent_OpenDNS_redirecting_Google_queries
I’ve found that forcing Google and Bing over to their “safesearch-only” sites is a very helpful parental control. I use HOSTS file for this purpose, but maybe OpenDNS can be set to provide this?
216.239.38.120 http://www.google.com #forcesafesearch
204.79.197.220 http://www.bing.com #forcesafesearch